ISO 27001 Testing Requirements + Checklist

- May 6, 2026
- Nabeesha Javed
“An audit is a spotlight on your security maturity.”
– ISACA
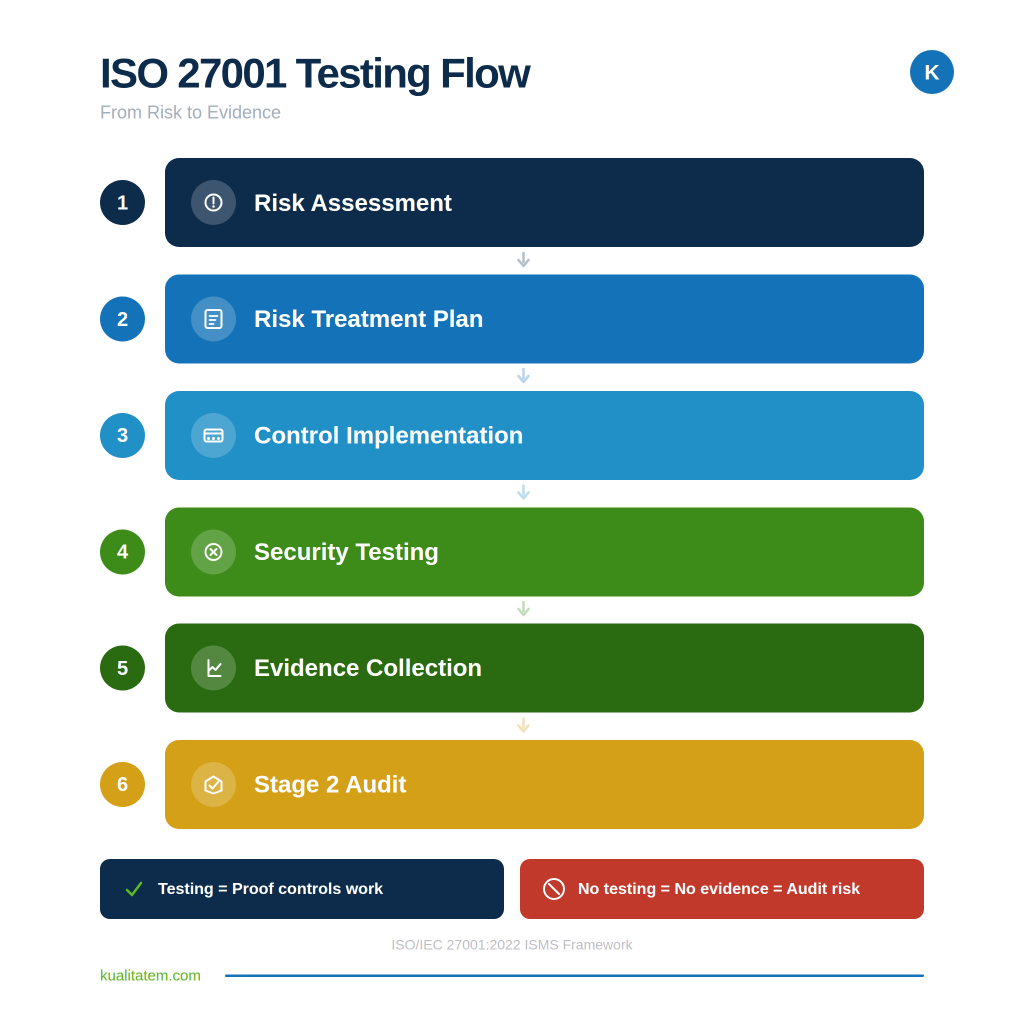
When audit season hits, auditors will demand evidence of technical vulnerability testing. Hand over a recent pen test report, documented risk assessment, and clean trail. If you have all three, the conversation is short. If you do not, you are looking at six weeks of scrambling to produce what should have been part of your security program all along.
And that scramble is expensive. Around 30% of ISO 27001 testing Stage 2 audits result in nonconformities tied to incomplete evidence, according to BSI and PECB data. When your certification costs somewhere between $15,000 and $100,000, a failed audit
- Waste that budget
- Delays the certification
So the real cost is not just the audit fee. It is the deal that stalls while you go back and fix what should have been done months ago.
Introduction to ISO 27001 Testing Requirements
ISO 27001 is the international standard for information security management systems. Over 58,000 organizations held certification as of 2021 (ISO Survey), with the number now estimated at 70,000+ across 150 countries based on 17-20% annual growth.
The standard itself does not hand you a checklist of specific tests to run. Instead, it requires you to build an ISMS (information security management system), identify risks, implement controls, and then prove those controls actually work.
That one part where most organizations fail is….
- Proving controls work means testing them.
And the standard gives you latitude on how you do that, which sounds like flexibility until you realize your auditor has specific expectations about what counts as proof.
The 2022 revision (ISO/IEC 27001:2022) consolidated the control set from 114 down to 93 and merged several testing-related controls into new categories. If your team is still working from the old structure, the mapping has shifted under your feet.
Overview of ISO 27001 Certification Process
The certification runs in two stages.
- Stage 1 is the documentation review, where the auditor checks whether your ISMS design meets the standard on paper.
- Stage 2 is where they verify that those controls are actually operating. That means interviews, evidence collection, and a hard look at your testing records.
After initial certification, you are on a three-year cycle. Annual surveillance audits in years two and three, then a full recertification audit.
The testing requirements do not disappear after Stage 2. They are ongoing, and auditors expect to see continuous evidence of assessment activity, not just a single report from a certification year.
If you want to get your organization certified as well, Kualitatem Consulting can help.
Book a CallImportance of Testing in Information Security Management
A control that has never been tested is a control you are hoping works. Hope is not evidence.
The whole architecture of ISO 27001 runs on a Plan-Do-Check-Act cycle.
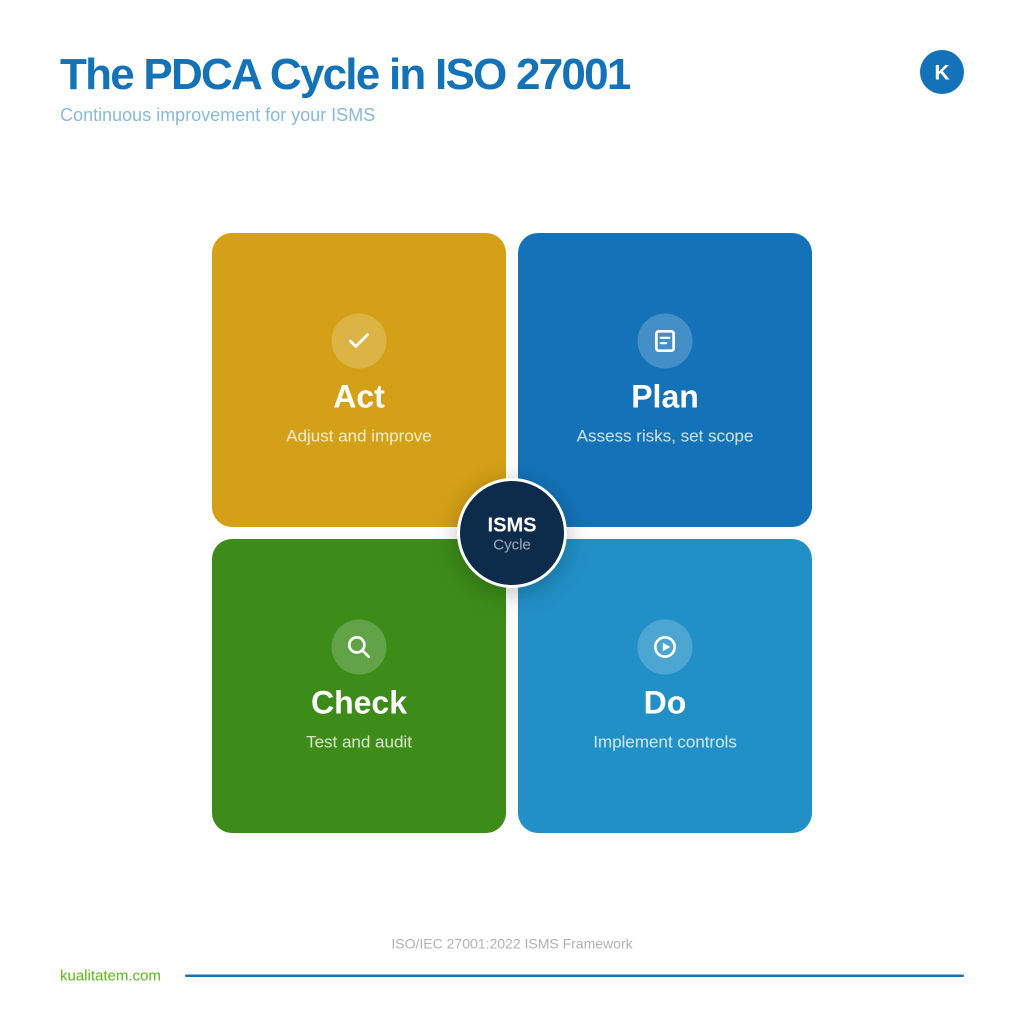
Testing is the Check. Without it, you cannot demonstrate continual improvement, which is a core principle that the auditor will evaluate. If your risk register says “external attack” is a threat and your treatment plan says “firewall rules and access controls,” the auditor will want to know:
- Who tested whether those actually stop an external attack?
That question is where penetration testing, vulnerability scanning, and security assessments enter the picture.
Read on How Kualitatem Helps EJADA Become ISO 27001
ISO 27001 Risk Assessment Requirements
| Conducting a Risk Assessment Clause 6.1.2 requires a formal risk assessment process. You need to identify information security risks, analyze their likelihood and impact, and evaluate which ones require treatment. This is not a one-time exercise. The standard expects you to reassess whenever there are significant changes to your systems, infrastructure, or threat landscape. | Risk Treatment Planning Your risk treatment plan documents the controls you are implementing for each identified risk. Annex A provides the control catalog. The Statement of Applicability (SoA) records which controls you selected and why. The auditor will cross-reference your SoA against actual evidence. If a control is listed as implemented but has no associated test or validation record, that is a nonconformity. |
The risk assessment is where testing requirements originate. If your assessment identifies “unauthorized access to production systems” as a risk, the treatment plan needs to include a way to verify that your access controls hold up. That verification is a test. The specific test depends on the risk, but the need for testing flows directly from this clause.
ISO 27001 Documentation Requirements
#1 Key Documents Needed for Certification
The documentation list is not short. At a minimum, you need:
- An ISMS scope statement
- Information security policy
- Risk assessment methodology
- Risk register
- Risk treatment plan
- Statement of Applicability
- Internal audit reports
- Management review minutes
- Corrective action records
- Evidence of control effectiveness.
That last item is the one most teams underinvest in.
Documentation is about having a traceable chain from identified risk to implemented control to test result to corrective action. Auditors follow that chain. If it breaks at any point, the audit pauses while you go find the missing link.
#2 Evidence Collection for Compliance
Evidence collection is where organizations burn the most time during an audit.
Screenshots of configurations, access control lists, penetration test reports, vulnerability scan outputs, patch management records, and incident response logs.
All of it needs to be current, organized, and mapped to specific Annex A controls.
Automated compliance platforms (Vanta, Drata, Sprinto) help with continuous evidence collection. But they do not replace the testing itself. A dashboard that says “control is monitored” is not the same as a report that says “we tested this control and here is what we found.”
Want to become ISO 27001 certified?
Does ISO 27001 Require Penetration Testing?
Understanding Penetration Testing in ISO 27001
The short answer: no, ISO 27001 does not explicitly mandate penetration testing by name. Not even after the 2022 revision.
The practical answer: your auditor will almost certainly expect to see one.
Here is the disconnect. The standard uses language like “technical vulnerabilities of information systems in use shall be obtained in a timely fashion” (Control 8.8, formerly A.12.6.1). The implementation guidance in ISO 27002:2022 specifically mentions penetration testing as one mechanism for meeting that intent. So while the word “penetration test” is not in the mandatory text, it is in the guidance, and auditors read the guidance.
ISO 27001 Penetration Testing Requirements
Two Annex A controls create the direct need:
Control 8.8 (Technical Vulnerability Management) requires you to identify technical vulnerabilities, evaluate exposure, and take appropriate measures. A penetration test is the strongest way to demonstrate that you have done this.
Control 8.29 (Security Testing in Development and Acceptance) is the 2022 merge of the older A.14.2.8 and A.14.2.9. It requires security testing during development, including code reviews, vulnerability scans, and penetration tests to identify weak coding and design.
If your risk assessment identifies external attack or unauthorized access as threats (and it should), a penetration test becomes the logical control. At that point, it stops being optional and starts being the expected evidence for your risk treatment plan.
Frequency of Penetration Testing: Annual or Otherwise?
The standard does not prescribe frequency. Best practice across the industry is at least once per year and after any major infrastructure change.
NIST guidance supports annual penetration testing supplemented by regular vulnerability scans.
Your risk assessment should define the cadence. If you are in financial services or healthcare, your regulatory environment may already demand quarterly or semi-annual testing. If your infrastructure is relatively stable and low-risk, an annual may be sufficient. The point is to have a documented rationale for whatever frequency you choose, not to default to “we do it once a year because that is what everyone does.”
ISO 27001 Security Assessment
Types of Security Assessments Required
Penetration testing is one piece. The broader security assessment landscape for ISO 27001 compliance includes:
• Internal audits (Clause 9.2) to evaluate whether the ISMS conforms to the standard and your own requirements
• Risk assessments (Clause 6.1.2) to identify and evaluate information security risks
• Technical vulnerability assessments to evaluate exposure across your infrastructure
• Security testing during development (Control 8.29), including code reviews, static analysis, and dynamic testing
• Management reviews (Clause 9.3) to evaluate ISMS performance at the leadership level
Vulnerability Scanning and Its Importance
Vulnerability scanning and penetration testing are not the same thing.
| Vulnerability Scan | Penetration Test |
| Automated process | Manual + automated approach |
| Identifies known vulnerabilities | Exploits vulnerabilities to test real impact |
| Compares systems against vulnerability databases | Simulates real-world cyberattacks |
| Surface-level detection | Deep, practical validation |
| Minimal human involvement | High involvement of skilled testers |
| Outputs a list of potential weaknesses | Provides verified vulnerabilities with impact analysis |
| May include false positives | More accurate with fewer false positives |
| Faster to perform | Takes more time |
| Requires less expertise | Requires high-level expertise |
| Shows what could be wrong | Shows what can actually be exploited |
Most organizations need both. Scans run frequently (weekly or monthly) to catch new vulnerabilities as they appear. Penetration tests run less often but provide deeper assurance that your controls actually stop an attacker, not just flag a CVE.
Conducting an ISO 27001 Internal Audit
The Internal Audit Process
Clause 9.2 requires internal audits at planned intervals. The purpose is to verify that your ISMS conforms to the standard and to your own policies. Internal audits must be conducted by someone independent of the area being audited. That does not mean you need to hire an outside firm, but the person running the audit cannot be the same person who built the controls.
A strong internal audit catches gaps before the external auditor does. The most expensive sentence in a certification audit is “we did not know about that.” Internal audits exist to make sure that sentence never comes out of your mouth.
Aligning Internal Audits with Testing Requirements
Your internal audit program should verify that testing is happening at the frequency your risk assessment defines. It should also check whether test findings are being tracked through to remediation. An internal audit that confirms “a pen test was conducted” but does not verify whether the findings were addressed is incomplete.
The link between testing output and corrective action is what auditors care about most. The test itself is just a discovery mechanism. The value is in what you did with the results.
Cloud Penetration Testing Requirements for ISO 27001 Compliance
Unique Considerations for Cloud Environments
Cloud environments introduce complexities in penetration testing that don’t exist in traditional on-premise setups. Major providers like Amazon Web Services, Microsoft Azure, and Google Cloud Platform enforce strict policies on what can and cannot be tested. In some cases, you must notify the provider in advance, while certain types of testing may be restricted altogether. Ignoring these rules and launching a test without reviewing the acceptable use policy can lead to serious consequences, including account suspension.
At the same time, the shared responsibility model defines clear boundaries. The cloud provider is responsible for securing the underlying infrastructure, while you are responsible for everything deployed on top of it. Your penetration testing scope must align with this division, focusing only on areas within your control.
Key considerations:
- Always review and comply with your cloud provider’s testing policies before starting
- Provide advance notification where required to avoid service disruption or penalties
- Align your test scope with the shared responsibility model
- Focus on testing your application layer, configurations, and access controls
- Avoid testing restricted areas such as the hypervisor or physical infrastructure
For ISO 27001, your ISMS scope determines what must be tested. If cloud services are included (which they typically are), your testing program must cover them. This requires either partnering with a firm experienced in cloud penetration testing or developing internal expertise to properly scope and execute these assessments.
What the Smart Move Looks Like
Organizations that pass ISO 27001 audits without unnecessary stress treat testing as an ongoing program not a last-minute checkbox. They build consistency into their approach, ensuring that security validation is part of regular operations rather than a reactive effort when an audit approaches.
What this looks like in practice:
- Running vulnerability scans on a consistent, scheduled cadence
- Conducting penetration tests at least annually and after major system changes
- Documenting findings and maintaining clear records
- Tracking remediation efforts through to closure
- Feeding results back into the risk register for continuous improvement
- Maintaining organized evidence so audits are straightforward, not reactive
When an auditor asks for proof, the response is structured and ready—not a last-minute scramble.
Kualitatem has been enabling this approach for over 16 years, delivering security assessments across banking, government, SaaS, and healthcare environments where assurance is critical.
Credentials that support this:
- Extensive experience across high-risk, regulated industries
- Compliance with ISO 27001 standards
- TMMi Level 5 certification
- A team of 250+ ISTQB-certified engineers
Next Steps for Your Organization
If your ISO 27001 certification or surveillance audit is coming up and your testing evidence has gaps, that is a solvable problem. But the window to solve it shrinks the closer you get to audit day.
Talk to Kualitatem. We will scope the assessment, run the tests, and hand you audit-ready documentation. Your team keeps shipping. We handle the security validation.
Book a Call









