What Could Go Wrong if IoT is not Tested Properly?

- March 30, 2026
- Nabeesha Javed
A connected thermostat locks 500 hotel rooms at 90°F for six hours. A fleet management sensor misreads GPS coordinates and reroutes 200 trucks into a toll zone. A wearable health monitor fails to flag abnormal heart rhythms because the firmware update broke Bluetooth sync on Android 14.
None of these are hypothetical. And none of them showed up in a test environment first.
If you’re a CTO with IoT anywhere in your product roadmap, the question isn’t whether you’ll ship defects. It’s how expensive those defects will be when they reach production. Bugs that cost $100 to catch in validation cost $10,000 to fix post-release. In regulated industries, multiply that by the compliance fallout.
The real cost isn’t the bug. It’s the blast radius.
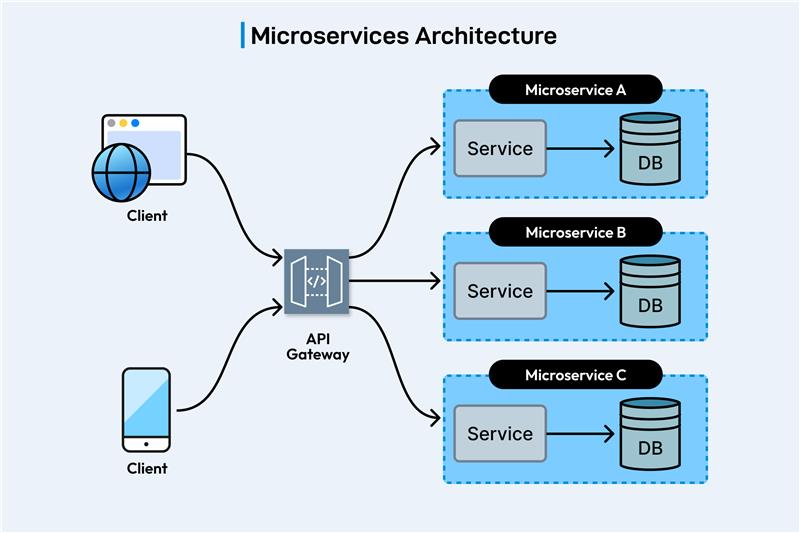
IoT failures don’t behave like software failures. A bug in a mobile app crashes the app. A bug in an IoT system cascades across the network.
One faulty node can corrupt data flowing between dozens of connected devices, triggering a chain reaction that renders the entire ecosystem unreliable. And unlike a software rollback, you can’t push a hotfix to a physical device sitting in a customer’s warehouse or strapped to their wrist.
The financial exposure here is concrete. Industry estimates peg the cost of recalling defective connected devices at roughly $10 million per year for mid-to-large enterprises. That’s not R&D budget. That’s brand damage, logistics overhead, legal exposure, and lost customer confidence packed into a single line item.
Coverage gaps multiply faster than your team can close them
Here’s where IoT breaks every assumption your validation process was built on.
A SaaS product runs on a browser. You test across Chrome, Safari, Firefox, a handful of screen sizes, and you’ve covered 95% of your user base. An IoT product runs on its own hardware, its own firmware, its own OS variant, and connects over Bluetooth, Wi-Fi, LTE, or Zigbee to devices you don’t control.
The smartphone market alone creates thousands of permutations: models, OS versions, chipsets, screen sizes, carrier configurations. Your connected device has to work reliably across all of them. Test ten combinations and you’ve barely scratched the surface. Skip coverage here and you’re shipping blind into the hands of users whose environments you’ve never simulated.
This isn’t a QA problem. It’s a business risk that compounds with every device you add to the ecosystem.
Connectivity failures that kill the user experience silently
An IoT system that loses connection doesn’t just pause. It degrades in ways that are invisible until a customer reports it or, worse, until it causes a downstream failure.
A dropped Bluetooth handshake between a sensor and its hub means data gaps. Data gaps mean inaccurate dashboards, missed alerts, or flawed automation triggers. For a smart home user, that’s an annoyance. For a logistics operation tracking cold-chain compliance, that’s a regulatory violation with audit consequences.
Most connectivity issues only surface under real-world conditions: interference, signal degradation, concurrent device load, firmware version mismatches. Lab environments don’t replicate these at scale. Without field-condition validation, your team is optimizing for a scenario that doesn’t exist in production.
Security exposure you didn’t budget for
Every connected device is a potential entry point. That’s not a theoretical risk statement. Over 70% of IoT devices currently in the market carry known security vulnerabilities.
Untested firmware creates openings for unauthorized access. Weak default credentials, insecure data transfer protocols, and unpatched update mechanisms give threat actors a surface area that grows with every device you deploy. In FinTech or healthcare, a single compromised endpoint can trigger a compliance event that costs more than the entire product line generates in a quarter.
The pattern is predictable: organizations invest heavily in application-layer security but treat device-level validation as an afterthought. That gap is where breaches happen.
What actually goes wrong: the pattern behind every IoT failure
Strip away the technical specifics and every IoT failure follows the same arc:
Insufficient device coverage leads to undetected compatibility issues. Those issues reach production. Users encounter failures that your support team can’t replicate because they never tested that device-OS-network combination. Resolution requires a firmware update that 40% of your installed base won’t apply for weeks. Meanwhile, negative reviews accumulate, support tickets spike, and your next board meeting includes a slide about product reliability you didn’t plan for.
Missing connectivity validation leads to silent data loss. That data loss corrupts analytics, triggers false alerts, or causes automation failures. By the time someone notices, the root cause is buried under weeks of bad data.
Skipped security validation leads to vulnerabilities that sit in production for months. A pen test at launch isn’t enough when firmware updates introduce new attack vectors every cycle.
Each of these compounds. And each one was preventable with the right validation strategy deployed early enough to catch it.
The fix isn’t more testing. It’s smarter coverage.
The answer isn’t throwing more devices at a manual QA team. It’s building a validation program that maps your actual risk surface and covers it systematically.
That means device matrices based on your real user telemetry, not theoretical market share. It means connectivity testing under degraded conditions, not just happy-path lab scenarios. It means security assessment baked into every release cycle, not treated as a one-time engagement.
Kualitatem has been doing exactly this across 2,000+ device configurations for enterprise IoT deployments. Our 250+ ISTQB-certified engineers build coverage strategies that match the complexity of your ecosystem, not just the scope of your QA budget. The result across our client base: 300% average ROI, with defect escape rates that drop measurably within the first release cycle.
Your next IoT release is the right time to fix this.
If your validation strategy was built for software and you’re now shipping connected products, the gap is already there. The question is whether you close it before production or after an incident.
Talk to our IoT testing architects and see what proper coverage looks like for your ecosystem.