Why You Need Micro Segmentation?

- November 7, 2016
- admin
Micro segmentation uses security technology and makes logical elements in data center and achieves them with advanced IT security policies and procedures. This whole process is performed in isolation on each node in order to limit any malicious activity in case the outdated security boundary is breached.
Proper segmentation can help you protect your confidential data in a network by way of applying standard security policies and rules. Through virtualization and control of software level in Network, micro-segmentation is used to control traffic of segmentation. Results derived from network segmentation are better network performance, virtualization, and software defined data centers, that are capable of handling workload more efficiently. Security rules and policies are applied to data center in units and vectors.
Micro-segmentation helps to enhance security in network; this is mainly required in networks to reduce the network surface attack by performing system segmentation. With the help of tools for traffic discovery, white listing the allowed traffic on server level and composing all the required variations is carried out to system level without interference.
The Software Defined Data Center (SDDC)
The SDDC is an approach and method to design data center, which influences a major standard of computer science and network concept. Operating systems, networking protocol, programming languages and server virtualization: all played vital roles in the industry innovation cycle over the past years.
The SDDC approach has been implemented in many major large Data Centers worldwide including Google, Amazon, and Facebook etc. In these huge Data Centers, engineers have deployed the SDDC abstraction layer into their platform and have customized the application; this helps them to automate every aspect of data center operations. Decoupling the whole underlying computing networks and storage hardware is also relevant in this regard. Decoupling reduces the expenses and operational costs of their physical infrastructure and delivers faster services in IT enterprise organizations.
SDDC is More Flexible, More Secure and More Agile
SDDC approach includes virtualization and automation, and it extends to entire data center build. Nowadays, an SDDC approach allows the whole IT system to programmatically create, delete, snapshot, and restore an entire data center construct of computing, storage, and networking in customized software. Automation of data center, self-service IT implementation, and complete transformation of network models can cause huge benefits to an SDDC. The SDDC approach facilitates the network structure and security team ability to achieve flexibility, protection, and utilization, which was never possible before in data center security. Security plays an important role in enforcing the application of SDDC platform in Agile environment.
Micro-Segmented Data Center Network
In the current era, the outdated network security strategies have become inefficient due to the modern techniques of security exploitation by hackers. In recent public breaches i.e. spear phishing, malware, social engineering; vulnerability exploits, etc. are a few examples of advanced security exploitation techniques used by hackers. In this regard, the micro-segmentation in the data center can be a vast help to stop and limit the illegal movement across the network.
Performance
To check the performance capacity of hardware, firewall platform is used to check and control traffic flowing from workload entering or leaving the data center.
Automation
The automation process and provisioning enables firewall policies to be provided with a workload that can be used or moved anywhere in the data center. This automation helps when any application is ever detected, deleted or removed from its security policy. This process eliminates the key obstacles, in deploying micro-segmentation.
Isolation
Virtual networks are different and isolated from the fundamental physical structure. Virtual networks after isolation can perform multiple workloads across the data center. In virtual network, isolation helps for allowing overlapping IP addresses but with the same underlying network infrastructure. Isolated development is possible with production and testing in virtual networks with different versions as well.
Segmentation
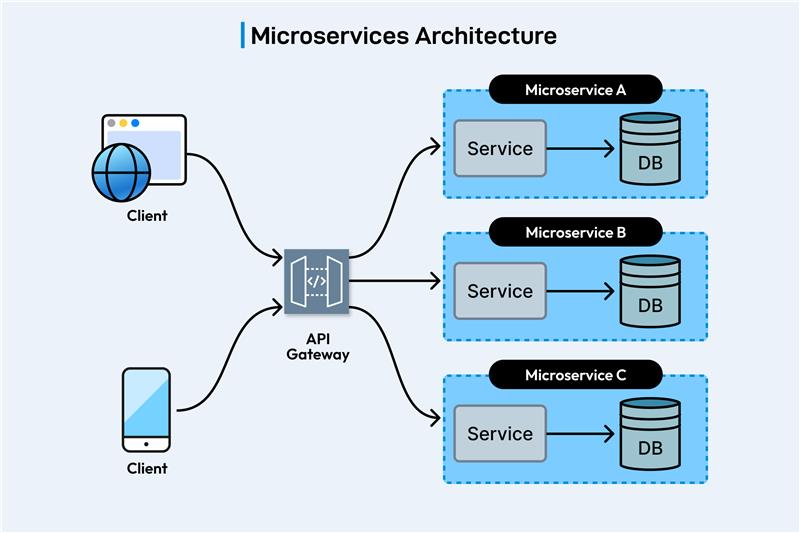
Segmentation is applied on multi-tier virtual network system, for a web, application, or a database tier. A virtual network supports multi-tier network infrastructure by applying L2 with L3 segmentation or micro-segmentation on L2 segment using workload firewall.
CONCLUSION
For better SDDC environment, the network virtualization platform has big opportunity for new operational models of security in data center or physical infrastructure.
This blog only scratched the upper surface of security infrastructure that is created with the help of deploying SDDC approach and network virtualization platform.