Security Testing for E-commerce Platforms

- January 26, 2026
- Malaika Saeed
The rise of e-commerce has revolutionized the way consumers shop, offering convenience and a vast array of choices.
However, this change has also attracted the attention of cybercriminals eager to exploit vulnerabilities in e-commerce platforms to gain unauthorized access to customer information.
To counter this threat, e-commerce businesses must prioritize security testing. It is a rigorous and comprehensive process that helps identify and rectify vulnerabilities in their systems.
In this technical guide, we will delve into the critical role of security testing in safeguarding customer information on e-commerce platforms, exploring various testing methodologies, tools, and best practices.
The Significance of E-commerce Security
E-commerce platforms handle a trove of sensitive customer data, including personal information, payment details, and purchase histories.
Ensuring the security of this data is not only crucial for maintaining customer trust but is also a legal requirement in many regions.
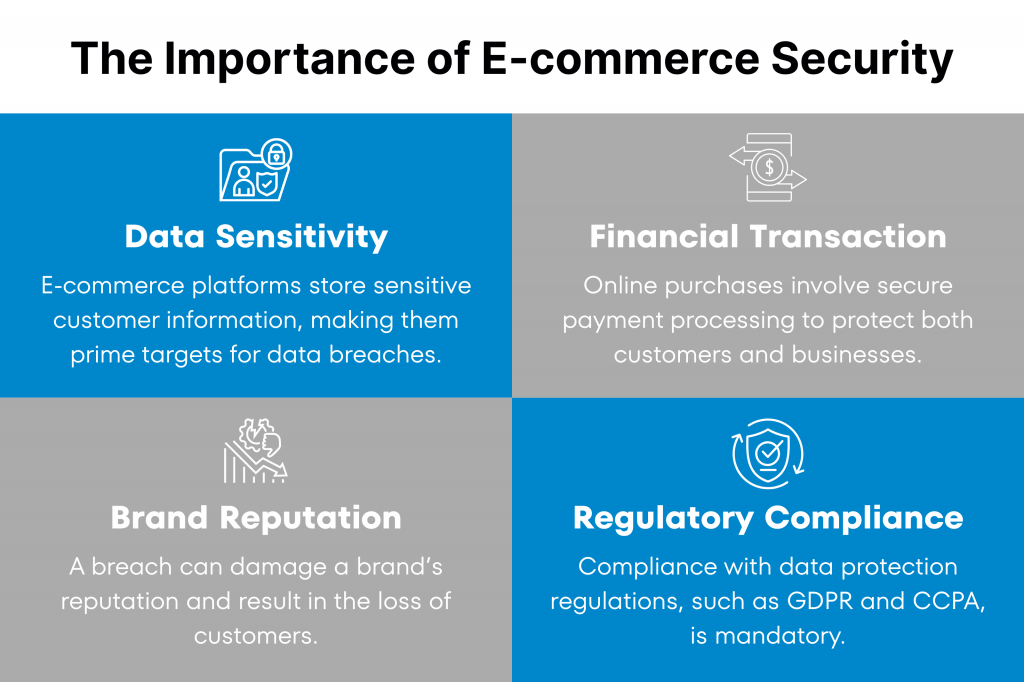
The key aspects that make e-commerce security imperative include:
- Data Sensitivity: E-commerce platforms store sensitive customer information, making them prime targets for data breaches.
- Financial Transactions: Online purchases involve financial transactions, requiring secure payment processing to protect both customers and businesses.
- Brand Reputation: A security breach can severely damage a brand’s reputation and result in the loss of customers.
- Regulatory Compliance: Compliance with data protection regulations, such as GDPR and CCPA, is mandatory, with severe penalties for non-compliance.
The Role of Security Testing
Security testing is an integral part of e-commerce security. It helps organizations identify vulnerabilities, assess security controls and ensure the confidentiality of customer information.
The primary objectives of security testing for e-commerce platforms include:
- Vulnerability Identification: Detecting and cataloging vulnerabilities within e-commerce systems, including web applications, databases, and payment gateways.
- Authentication and Authorization Testing: Assessing access controls to prevent unauthorized access to customer data.
- Payment Security Assessment: Ensuring the secure processing of payment information to prevent fraud and data breaches.
- Data Encryption Validation: Verifying the encryption of sensitive data in transit and at rest to safeguard against interception and theft.
- Security Patch Management: Identifying and applying security patches to address known vulnerabilities.
Key Security Testing Methodologies
E-commerce security testing encompasses a range of methodologies tailored to assess different aspects of security.
Below are some key security testing methodologies commonly employed to safeguard
customer information.

1. Vulnerability Assessment
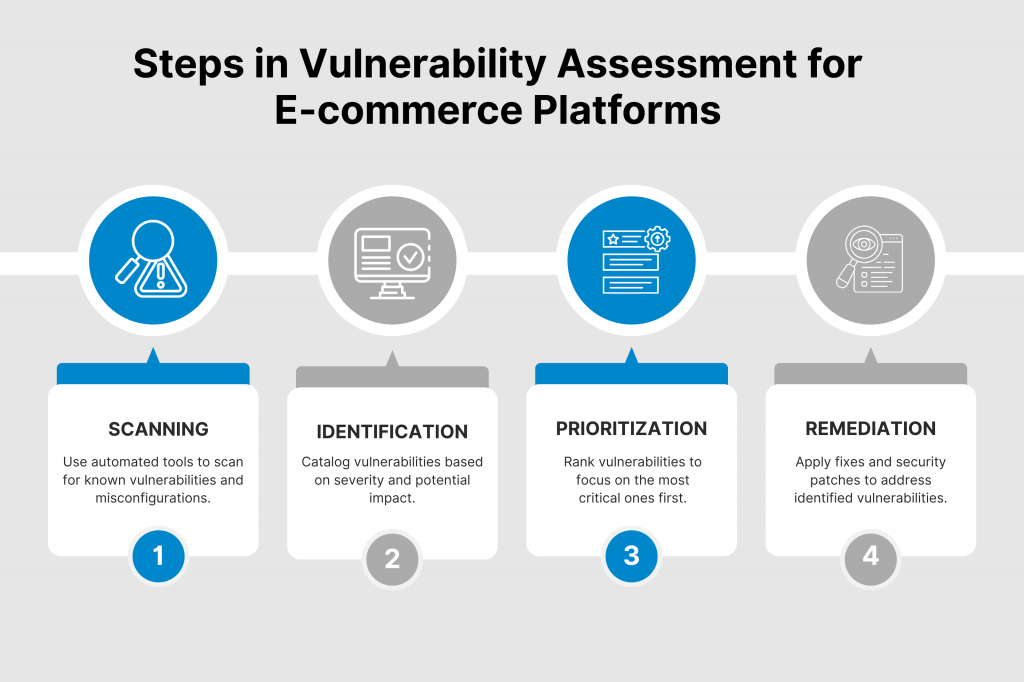
Vulnerability assessment involves the systematic identification of vulnerabilities within the e-commerce platform.
Key aspects of vulnerability assessment include:
- Scanning: Automated tools scan the platform’s infrastructure, networks, and applications for known vulnerabilities and misconfigurations.
- Identification: Cataloging vulnerabilities based on their severity, potential impact, and ease of exploitation.
- Prioritization: Assigning priorities to vulnerabilities to focus remediation efforts on the most critical issues.
2. Penetration Testing
Penetration testing, also known as ethical hacking, simulates cyberattacks to identify weaknesses in e-commerce systems.
The main aspects of penetration testing include:
- Targeted Attacks: Simulating real-world attacks to assess an organization’s defenses and response capabilities.
- Exploitation: Attempting to exploit vulnerabilities to gain unauthorized access and provide actionable recommendations for remediation.
- Security Control Validation: Evaluating the effectiveness of security controls and configurations.
3. Web Application Security Testing
Web application security testing focuses on identifying vulnerabilities in the e-commerce platform’s web-based components.
- Aspects of web application security testing include:
- Web Application Scanning: Assessing web applications for common vulnerabilities such as SQL injection, cross-site scripting (XSS), and cross-site request forgery (CSRF).
- Authentication and Authorization Testing: Evaluating access controls and user privileges to prevent
unauthorized access. - Session Management Testing: Verifying the security of user sessions to prevent session hijacking.
4. Payment Security Assessment
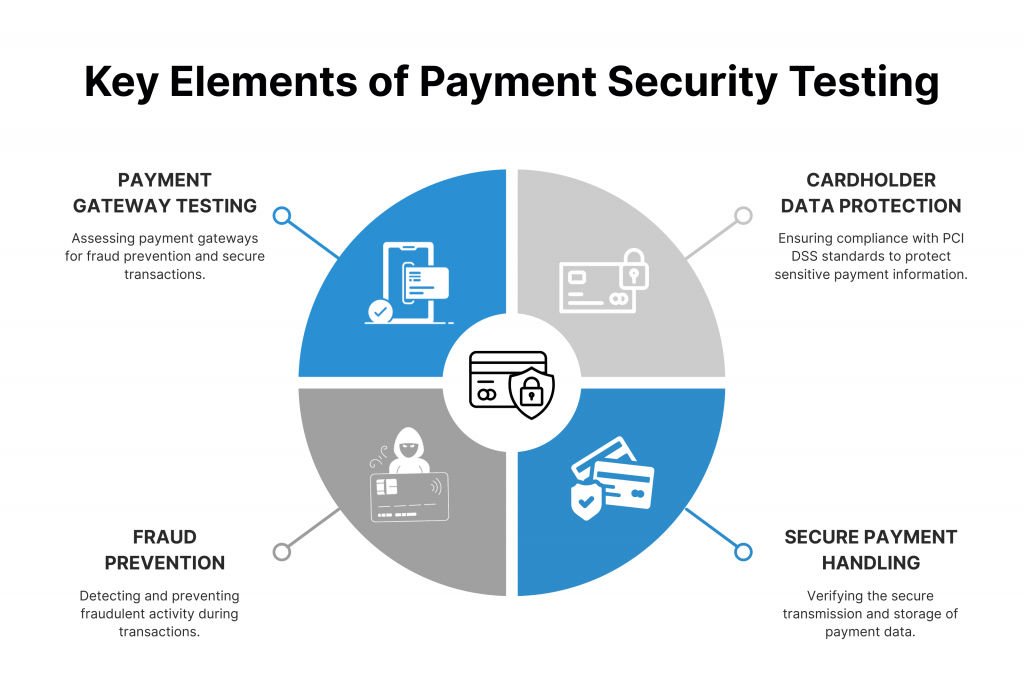
Payment security assessment specifically examines the secure processing of payment information within the e-commerce platform.
The process includes:
- Payment Gateway Testing: Assessing the security of payment gateways to prevent fraud and ensure secure transactions.
- Cardholder Data Protection: Ensuring compliance with Payment Card Industry Data Security Standard (PCI DSS) requirements.
- Secure Payment Handling: Verifying that payment data is securely handled and transmitted.
5. Network Security Testing
Network security testing evaluates the security of an organization’s network infrastructure, including firewalls, routers, and switches.
This type of testing usually does:
- Firewall Assessment: Identifying weaknesses in firewall configurations and rule sets.
- Network Scanning: Scanning the network for open ports, vulnerabilities, and potential entry points.
- Intrusion Detection and Prevention Testing: Evaluating the effectiveness of intrusion detection and prevention systems (IDS/IPS).
Best Practices in E-commerce Security Testing
To effectively safeguard customer information on e-commerce platforms, organizations should adhere to best practices that ensure comprehensive assessments and risk mitigation, which are as follows.

Comprehensive Testing
Implement a comprehensive security testing program that covers all aspects of the e-commerce platform, including web applications, payment processing and network infrastructure.
Regular Assessments
Perform security assessments regularly to identify and remediate vulnerabilities in a timely manner. The frequency of testing should align with the pace of change in your environment.
Threat Modeling
Conduct threat modeling to identify potential threats and attack vectors specific to your e-commerce platform and customer data.
Secure Development Practices
Promote secure development practices among development and IT teams, emphasizing secure coding, secure configurations and adherence to security standards.
Remediation Planning
Develop a structured remediation plan that prioritizes vulnerabilities based on their potential impact and ease of exploitation. Ensure that vulnerabilities are addressed promptly.
Continuous Monitoring
Implement continuous monitoring to detect and respond to security incidents in real-time. This includes intrusion detection, log analysis, and security information and event management (SIEM) solutions.
Security Awareness Training
Invest in security awareness training for employees to educate them about the risks to customer information and their role in mitigating those risks.
Conclusion
The security of customer information on e-commerce platforms is paramount, both for maintaining trust and complying with regulations.
Security testing plays a pivotal role in identifying vulnerabilities, assessing security controls, and ensuring the integrity of customer data.
By implementing comprehensive security testing methodologies and adhering to best practices, e-commerce businesses can fortify their defenses against cyber threats. This way, they can also protect the sensitive information of their customers.
Kualitatem’s experts perform in-depth security testing on your e-commerce platforms. Reach out today to get a free quote and process overview.











