Security Risks in Identity & Access Management Software

- December 26, 2025
- Malaika Saeed
Cyber criminals keep on finding new ways to carry out attacks. To combat this growing threat, companies must make it a top priority to avoid these attacks and minimize any damage they cause.
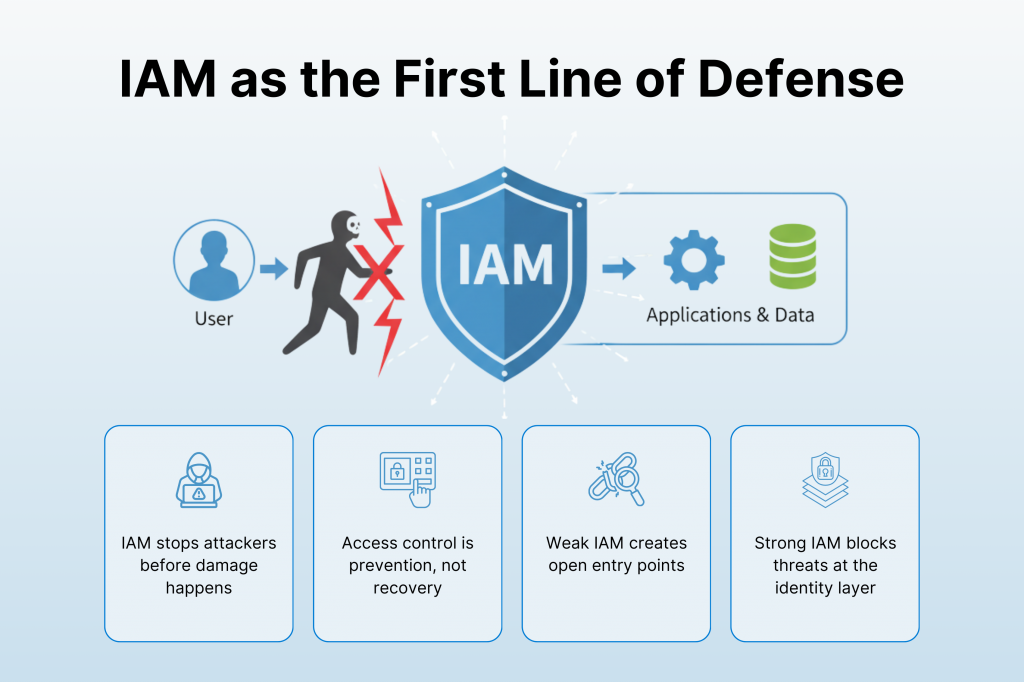
An often-overlooked approach is to stop hackers from obtaining access in the very first place. This proactive strategy is crucial because once a hacker gains access, the damage can be significant.
Identity Access Management (IAM) is a valuable tool that your IT team can use to prevent unauthorized access to your company’s SaaS app data, systems, or networks.
However, it is critical to be mindful of the hazards that may develop if access and identity management are not properly established.
Many common identity and access management errors can lead to security vulnerabilities. These include granting users access to unauthorized data and allowing logins from unauthorized IP addresses. Exposing APIs can also pose significant risks.
Thus, to get over this issue, your firm can move forward with a leading software testing company with experts for different testing processes to get rid of the potential challenges and risks your firm can possibly go through.
Key Takeaways
- IAM is a frontline security control that prevents attackers from gaining access before damage happens.
- Poor IAM setup like over permissioned users, exposed APIs, weak passwords or missing MFA is a major cause of breaches.
- IAM improves productivity and compliance at the same time by giving the right people the right access only when needed.
- Insider threats and misconfigurations are real risks and need continuous monitoring, access reviews, and automation.
- Regular security testing and expert validation are critical to catch IAM gaps early before attackers exploit them.
What is Identity and Access Management Software?
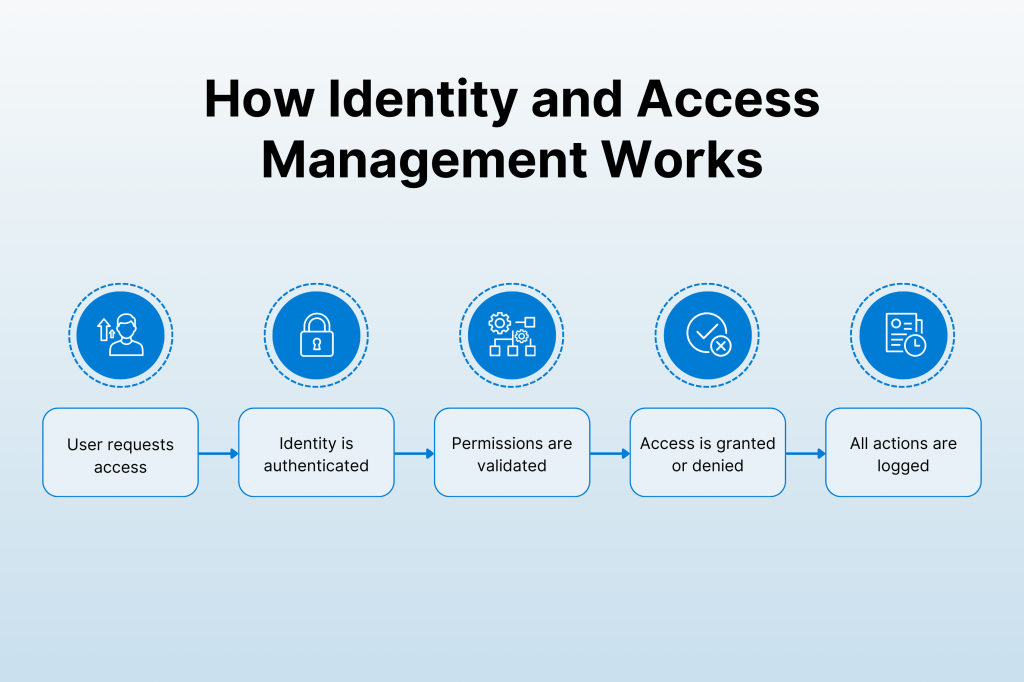
Identity and Access Management (IAM) technology is an organization’s structure that includes processes, policies, and technology for efficiently managing electronic or online identities within a company.
It is intended to limit user access to vital data and assets while adhering to security and compliance guidelines.
IAM systems like Amazon Web Services (AWS) allow you to create individuals, groups, roles, and privileges within your organization’s digital environment.
Businesses that deploy IAM software may ensure that the proper people have access to diverse systems and data, lowering the risk of illegal access and security breaches.
These solutions play an important role in cybersecurity since they regulate user privileges and access to protect sensitive information.
Importance of IAM
Identity and Access Management (IAM) manages user identities, company resources, and the allocation of access and authority in the digital system to ensure that the right user handles the right data or resource. IAM offers several important benefits:
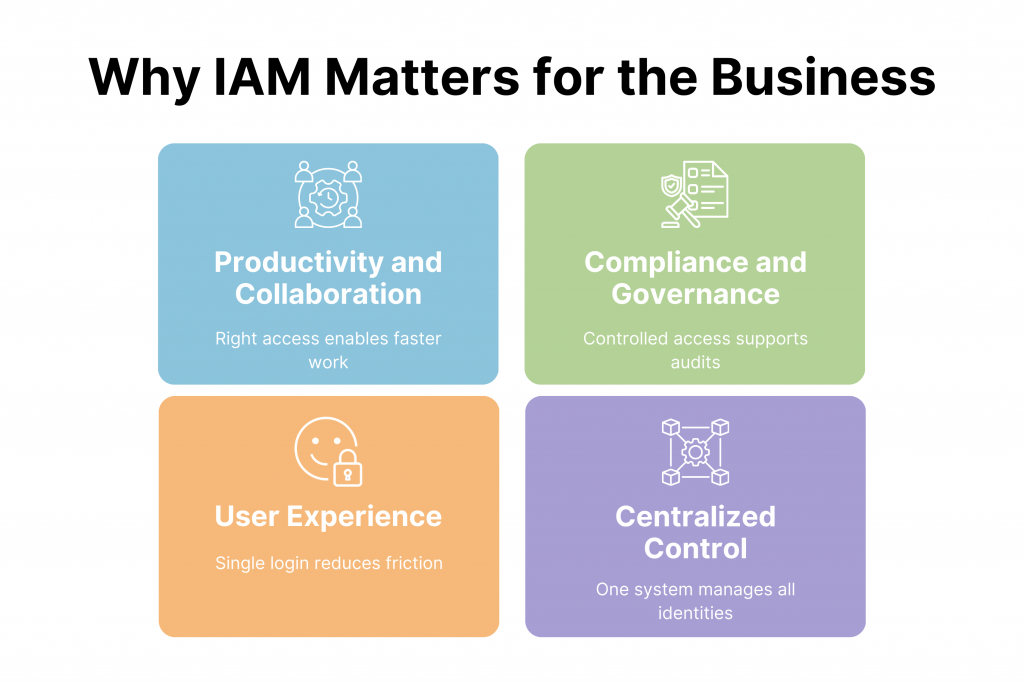
Productivity and Collaboration
IAM allows businesses to seamlessly collaborate with other enterprises, guests, and contributors. This leads to increased productivity and smoother operations in the office.
Tasks that used to take a long time due to physical processes such as filling out and submitting forms can now be accomplished faster.
Tasks can be completed in minutes by delegating to others, such as writers or guests. IAM grants limited access to both types of profiles (contributors and guests).
These accounts are granted permission to hasten the fulfillment of work goals. However, higher-level resources are locked and made unavailable to guests or identities that don’t need access.
IAM and Compliance
IAM facilitates compliance by limiting access to certain personnel. Meanwhile, others have limited access to critical data.
Compliance entails not only getting hold of new technology and techniques, but also their effective application for the intended purpose.
IAM incorporates division of duties (SoD) and the principle of least privilege (PoLP) when needed. This technique actively protects data sensitivity while also preventing fraud and identity theft.
Improved User Experience
Organizations that use multiple platforms or have a growing list of applications will have to enter users, emails, and passwords many times.
With IAM, a single login via single sign-on (SSO) provides access to all relevant resources. This saves time and minimizes stress, resulting in greater efficiency and a smoother user experience.
Centralized Control Point
IT administrators may automate and handle all user profiles using a single interface. This centralized control point reduces the labor associated with manual one-on-one handling of every user’s account.
This centralized interface boosts productivity while allowing the IT staff to install more preventative security features.
Data Security and Identity
A digital workspace with working from home jobs has heightened the risk of theft of information in the twenty-first century workplace.
Previously, all the company’s data, tools, and assets were maintained in an isolated building. Local networks allow company PCs to access material stored in local databases.
Employees can access data from any system or their personal laptops without any problem. This raises the risk of theft of identities and data breaches in the firm.
There hasn’t been a more crucial time to develop a comprehensive IAM system, with security being the most important benefit.
Potential Risks in Identity and Access Management Software
As IAM has made the work easier for different companies it has also increased the risk of exposing companies to different dangers of data breaches and cyber-attacks.
The following are the major risks in IAM.
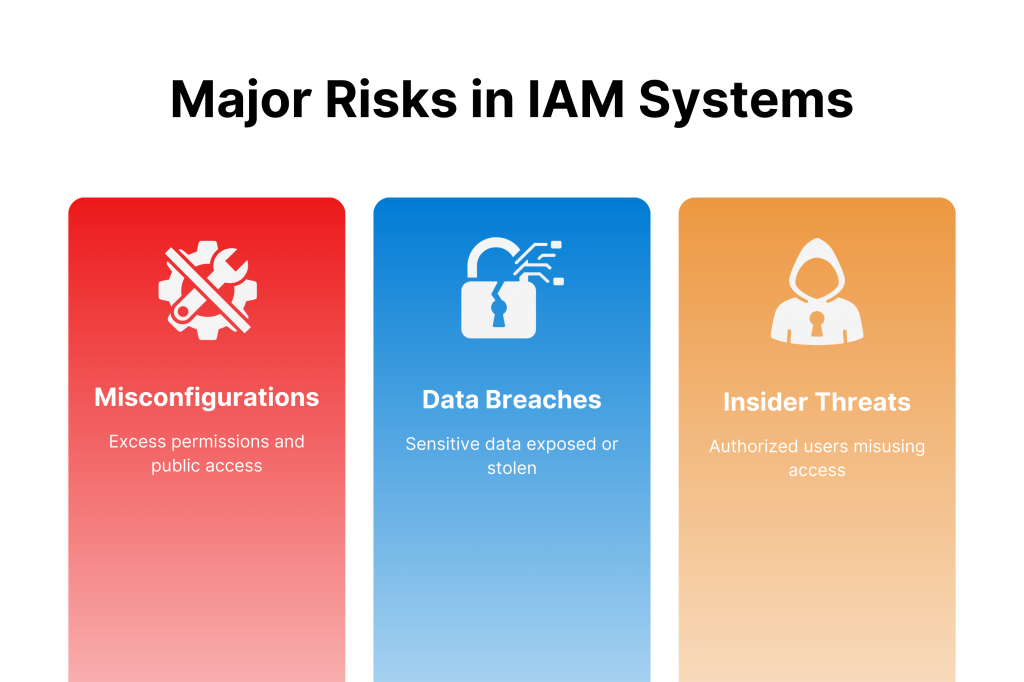
Identity Misconfiguration
Identity misconfigurations can take the form of permitting logins from unknown individuals or IP addresses, keeping APIs or datastores available to the public, not using MFA, not rotating access keys regularly, or not controlling data access. Misconfigurations are a major cause of environmental breaches.
Cloud Security Posture Management technologies are the premier option for detecting and resolving any misconfigurations that put environments at risk.
They operate by constantly tracking audit records and behavior and comparing it to a secure baseline.
Data Breaches
IAM systems might be targeted in breaches of data, exposing sensitive information. This can have serious consequences, including monetary losses, governmental penalties, and a loss in consumer trust.
Did You Know?
Deloitte, one of the world’s “big four” accounting firms, had a cybersecurity assault in 2017. The consulting firm was one of the largest in the US, offering cybersecurity advice to government agencies, banks, and global corporations. They had access to sensitive financial and personal information.
Deloitte’s $37 billion (about $110 per person in the US) revenue in 2017 provided ample resources for implementing a sophisticated security system. Hackers easily bypassed it with a simple password compromise. Hence, how did the attackers accomplish it?
The hackers accessed Deloitte’s global email system through an administrator account.
Insider Threats
Insider threats pose a substantial risk to IAM systems. These threats include personnel abusing their access rights, exploiting system vulnerabilities, or purposefully gaining unauthorized access to sensitive resources.
Insider attacks can pose a significant security risk to an organization if appropriate safeguards are not in place.
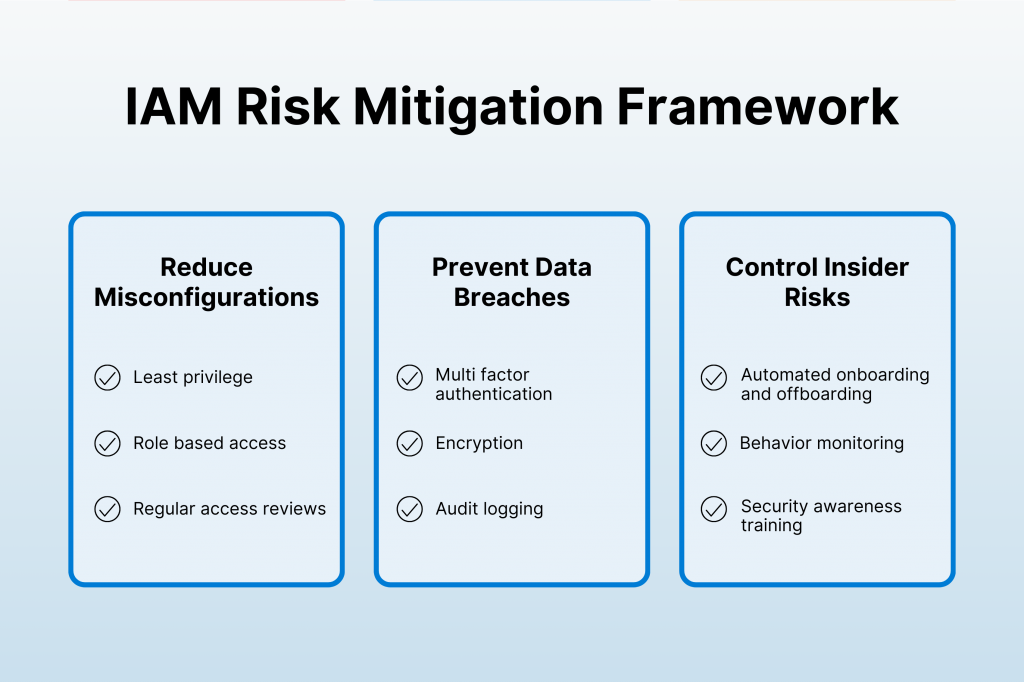
Strategies to Mitigate Risks of IAM
To mitigate the risks it is necessary to apply different tests to your software or system. It helps to make sure your system is not vulnerable to threats. Here are a few mechanisms you can apply to get over these risks.
1. For Misconfigurations
Least Privilege Principle
Assign the minimum necessary permissions to users, granting access only to the resources they require for their roles. This reduces the risk of accidental or intentional misuse.
Role-Based Access Control (RBAC)
Define roles based on job responsibilities and assign permissions accordingly. RBAC simplifies access management and ensures consistency.
Regular Access Reviews
Conduct periodic reviews of user access rights. Remove unnecessary permissions and validate that access aligns with current roles and responsibilities.
Centralized Identity Management
Use a single system to manage user identities across applications and services. Centralization improves efficiency and reduces the risk of inconsistencies.
Automated Tools
Use automated tools to monitor and manage configurations. These tools can alert you to any changes that could create potential vulnerabilities.
2. For Data Breaches
Multi-Factor Authentication (MFA)
Require users to authenticate using multiple factors (e.g., password and a one-time code sent to their phone). MFA significantly enhances security.
Strong Password Policies
Enforce strong password policies, including password complexity requirements and regular password changes.
Encryption
Encrypt sensitive data at rest and in transit. This protects information from unauthorized access.
Audit Trails and Logging
Monitor and log all access attempts. This helps detect suspicious activity and provides an audit trail for investigations.
3. For Insider Threats
Automated Provisioning and Deprovisioning
Automate user onboarding and offboarding processes. This ensures timely access provisioning and prevents lingering access after an employee leaves. Lingering access can lead to insider threats.
Education and Training
Regularly train employees in security best practices, emphasizing the importance of safeguarding their credentials.
Investigate Unusual Activity
Monitor user behavior and investigate any anomalies. Detecting unusual patterns early can prevent potential threats.
Closing Thoughts
Where IAM has made accessibility easier, it has brought many challenges for the IT teams as well.
To get some ease of mind being an employer, it’s recommended that you choose the expert teams who are professionals to solve these challenges for you.
So, without giving it a second thought, contact Kualitatem now!
Frequently Asked Questions (FAQs)
Q1) What is the difference between IAM and SSO?
IAM controls who gets access to what and under which conditions. SSO is one feature within IAM that lets users log in once to access multiple systems.
Q2) How does IAM help with regulatory compliance?
IAM enforces least privilege and segregation of duties. This helps organizations meet standards like ISO 27001, SOC 2 and GDPR with clear access controls.
Q3) What are common IAM misconfiguration risks in cloud environments?
Typical risks include over permissioned roles, public APIs, unused access keys and disabled MFA. These gaps are a leading cause of cloud data breaches.
Q4) Why is security testing important for IAM systems?
IAM testing helps uncover access loopholes, privilege escalation risks and policy flaws. It ensures identities are secured before attackers exploit them.











