Meet Our Leadership Team
Board

JAMIL GOHEER
(Founder and Chief Executive Officer)Jamil’s career spans over 15 years setting up and scaling technology businesses. He co-founded Kualitatem in 2009 to help enterprises and SMEs ensure technology rollouts that are timely and free of defects. Kualitatem is a leading independent software quality assurance and information security consulting company with customers from Fortune-1000 companies. He has also been involved in setting up an innovative venture fund based from New York called CoVenture, and a specialized product engineering company called Virtual Force. Prior to this he was involved in a venture-backed speech technology startup identifying languages from speech signals. He also serves on the Board of a Swedish Health Tech company providing online specialist care.
Jamil is a Certified Information System Auditor (ISACA) and has been consulting with international organizations like UNESCO, CIDA, UNDP, GTZ, Nike and Foundation for Development Cooperation Australia, enabling growth through technology. He also teaches and speaks on entrepreneurship in academic settings. He received his BS degree from FAST, Masters degree from LUMS and took a leadership program at Clare College Cambridge.

KHURRAM MIR
(Co-Founder and Chief Marketing Officer)Khurram Mir, as CMO, is leading the marketing and sales team at Kualitatem with his extensive QA expertise. He has worked as a QA, consulting and advising expert for clients helping them in their QA pursuits. He has been instrumental for Kualitatem with his 10+ years of experience in the software testing space. Khurram co-founded Kualitatem with a passion to promote independent testing as a mandatory step in a development lifecycle keeping in view the known problems and dilemmas faced by QA departments.
His skill set spans requirement verification and validation, design time controls and test plans, writing test cases, generating test reports and bug reports and conducting audits. He likes to address the pain points of clients while educating them about the latest testing trends and how their application can help them in releasing immaculate software. Khurram holds a bachelors in computer sciences and a master’s in business administration. He is an avid traveler and mountaineer.

SOHAIL KHAN
Sohail Khan is a seasoned business executive in high tech with versatile experience. Leading startups, he has transformed them into multi-billion dollar enterprises. He has a track record of anticipating and developing new technologies to expand on market opportunities and generating shareholder value.
Sohail has been involved in extensive M&A, IPO and Fund Raising Experience, executed over $5B of transactions on a global basis and raised over $50M in equity/debt financing. He served as a CEO and head of strategy for various companies. In these experiences, he took Agere Systems to IPO, filed S1 for SiGe Semiconductor and fund-raised through private placement for ViXS Systems. He is experienced in Corporate Governance, having served on the Boards of public as well as private companies including audit, compensation and finance committees. He graduated as an engineer and later took an MA degree from the University of California, Berkeley.
Management Team

Jamil Goheer
(Founder and Chief Executive Officer)Jamil’s career spans over 15 years setting up and scaling technology businesses. He co-founded Kualitatem in 2009 to help enterprises and SMEs ensure technology rollouts that are timely and free of defects. Kualitatem is a leading independent software quality assurance and information security consulting company with customers from Fortune-1000 companies. He has also been involved in setting up an innovative venture fund based from New York called CoVenture, and a specialized product engineering company called Virtual Force. Prior to this he was involved in a venture-backed speech technology startup identifying languages from speech signals. He also serves on the Board of a Swedish Health Tech company providing online specialist care.
Jamil is a Certified Information System Auditor (ISACA) and has been consulting with international organizations like UNESCO, CIDA, UNDP, GTZ, Nike and Foundation for Development Cooperation Australia, enabling growth through technology. He also teaches and speaks on entrepreneurship in academic settings. He received his BS degree from FAST, Masters degree from LUMS and took a leadership program at Clare College Cambridge.

Khurram Mir
(Co-Founder and Chief Marketing Officer)Khurram Mir, as CMO, is leading the marketing and sales team at Kualitatem with his extensive QA expertise. He has worked as a QA, consulting and advising expert for clients helping them in their QA pursuits. He has been instrumental for Kualitatem with his 10+ years of experience in the software testing space. Khurram co-founded Kualitatem with a passion to promote independent testing as a mandatory step in a development lifecycle keeping in view the known problems and dilemmas faced by QA departments.
His skill set spans requirement verification and validation, design time controls and test plans, writing test cases, generating test reports and bug reports and conducting audits. He likes to address the pain points of clients while educating them about the latest testing trends and how their application can help them in releasing immaculate software. Khurram holds a bachelors in computer sciences and a master’s in business administration. He is an avid traveler and mountaineer.

Kashif Abid
(Head of Security)With an experience of more than 10 years in the field of information security, Kashif boasts quite a diverse portfolio. Kashif holds certifications for Certified Ethical Hacker (CEH), EC-Council Certified Security Analyst (ECSA), CCNA, CCNP, M.C.P and M.C.S.A (Messaging). After completing his masters from the National University of Science and Technology, Islamabad, Pakistan he has been involved with various public and private organizations in the areas of information technology and security and also been attached with academia for the last six years. He has also been providing training in coordination with DFID, USAID and private sector universities.
At Kualitatem, Kashif heads security and compliance activities. He excels in network/computer systems penetration to look for weaknesses and vulnerabilities in target systems. Moreover, he also supervises successful deployments of security solutions, penetration testing activities and information security auditing. Kashif believes in practicing his beliefs in imagination and innovation with confidence. Technology products that make human lives better deeply interest him.

Uzma Yasin
(Head of QA)Uzma Yasin holds a diverse experience of more than 10+ years in the QA industry. She holds a bachelor’s degree in computer sciences and a master’s degree in business administration. Uzma excels in preparing, writing and reviewing test cases. Uzma excels in creating corporate marketing strategies, plan development, collateral development for marketing campaigns and product overview brochures.
At Kualitatem, she leads the QA team. Leading the QA team she is responsible for all testing activities, client liaison, internal and external reporting and project deliveries. She also leads all defect management, code analysis, requirements gathering, acceptance testing, regression testing, functional testing and performance testing activities at Kualitatem. She is interested in QA related topics, particularly the ones, that aid in creating applications with minimum errors and defects.

Nadia Irfan
(Head of Process Excellence)Nadia Irfan is an industry veteran in the areas of Quality Assurance, Testing Methodologies and Process Management. She is a seasoned professional with more than 20 years of experience in Transforming Quality Management Functions using varied frameworks and lifecycle models. She Headed and Directed Quality Assurance and Process Engineering departments as Quality Leader. Managed Testing Services for Fortune 500 companies and established Software Process Improvements using standards like ISO TickIT, IEEE, CMMI, TMMi etc. At Kualitatem, she leads the Process Excellence Team to ensure the quality of our internal processes and to maintain the standardization in all Testing Practices by using best industry frameworks and Methodologies like TMMi.
She holds a BSc honors degree in electrical engineering from University of Engineering and Technology Lahore. In addition to various other professional certifications she is a CSTE and PMP Certified Professional. In her free time, she likes to read, paint and spend time with family.”
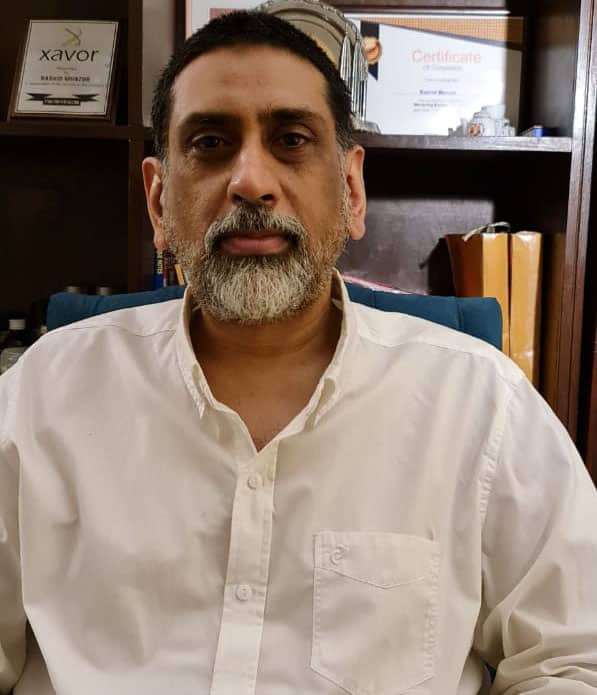
Rashid Munzur
(Head of Program Management Office)Rashid brings with him 20 years of rich and diversified experience armed with managing medium to large enterprise strategic projects from multiple domains which are ranging from IT, Finance and Commercial products and services launch. He has a track record of organization-wide process alignment and change management, amid fast changing industry needs. He has served as Head of Program Management Office (PMO) in Wateen Telecom, the Abu Dhabi Group’s communication venture in Pakistan and also as a Quality Assurance Manager in Xavor Corporation. Over the years he has worked in various strategic projects such as Standard Chartered Bank (Hong Kong) B2B portal and WiMAX Relaunch.
Rashid did his MBA from School of Business & Commerce, Preston University and BSc Computer Sciences from The Institute of Management Sciences – Pak Aims.

Ahmad Sardar
(Head of Innovation and Strategy)Ahmad is a product innovation expert who brings with him a diverse leadership experience in the areas of strategy, innovation, product development and operations, and has worked in both IT and Telecom Industries. In his 15 years of experience he has worked on developing growth and competitive strategies, making and launching new products, setting up innovation platforms within organizations and managing mobile network operations. Ahmad has hands-on experience in product development in SAAS, mobile Apps and multi-user consumer platform Apps.
Ahmad has done his MBA from INSEAD (France) and Bachelors from GIKI in Electronics Engineering.

TARIQ RASHID
(Chief Operating Officer)Mr. Tariq Rashid is Chief Operating Officer at Kualitatem. With more than 30+ years of experience in Management & Information Technology, he has worked as VP & Chief Strategy Officer at Jazz, Board Director at Mobilink Microfinance Bank, and served multiple other notable roles, including Chairman of (Human Resources and Compensation Committee) HRCC, (United Bank Limited) UBL, and (Board IT Committee) BITC.
He holds an engineering degree from the University of Engineering and Technology (UET), Lahore, and a post-graduate certificate in Computers from National Academy of Higher Education. He has completed management programs abroad and locally from institutes like IMD, INSEAD, MIT, Harvard, and LUMS.
Advisors

Abdul Razzak Dawood
Razak Dawood founded Descon Engineering Limited that evolved into a leading engineering firm in Middle East and Pakistan. He served in various roles including Managing Director Lawrencepur Textile Mills and Dawood Hercules Chemicals Limited and Director United Refrigeration Industries (pvt) Limited.
He served as Federal Commerce Minister and has been serving as Advisor for Commerce, Textile, Industry and Production, and Investment of Pakistan since 2018. Mr. Dawood has been an active philanthropist and currently he is the Rector, Lahore University of Management Sciences; Vice Chairman, Board of Governors, National Management Foundation; Member, Board of Governors, Shaukat Khanum Cancer Hospital and Research Centre. Mr. Dawood is a BSc. Mining Engineering from England and MBA Columbia University, USA.

Naeem Zafar
Naeem is co-founder and CEO of TeleSense, an IoT (Internet of Things) startup in the AgTech space, that is addressing remote monitoring and control of post-harvest grain. Previously he served as the CEO of Bitzer Mobile (Acquired by Oracle in November 2013). He also teaches entrepreneurship at the University of California Berkeley.
Naeem started his own business at the age of 26 and subsequently went on to start and work at six startups. His first job out of Brown University with a degree in electrical engineering was to design chips and electronic systems. Twenty years, two kids, one IPO and three CEO stints later, he founded Startup-Advisor, a company focused on educating and advising entrepreneurs on all aspects of starting and running a business (www.Startup-Advsior.com ).
